

.svg)
.svg)
The pandemic and ever-increasing threat of cyberattacks have given new urgency to public sector digital transformation. Demand for cloud service products in the FedRAMP marketplace increased 60 percent year-over-year in the first half of 2021. Federal agencies are looking to modernize, shifting away from maintenance-heavy legacy apps to modern, scalable cloud applications. To improve security and user experience, they need cloud service providers (CSPs) who have proven their ability to safely handle federal data.
Enter FedRAMP. The Federal Risk and Authorization Management Program, FedRAMP, defines baseline security standards — including regular security assessments, continuous monitoring and data access — for U.S. federal agencies’ cloud services.
Understanding FedRAMP impact levels is critical for organizations interested in modernizing their cloud security frameworks to keep up with evolving threats, ensure regulatory compliance, and adopt the latest tools for their constituents.
FedRAMP’s risk-based assessment program protects federal data and minimizes the impact on individuals or organizations if data is compromised. FedRAMP’s standardized impact levels also make it easier for government agencies to assess whether a CSP has sufficient security and data protection capabilities for the data they handle.
Under FedRAMP, cloud services are separated into three classifications: Low Impact Risk, Moderate Impact Risk and High Impact Risk. FedRAMP security requirements apply government-wide and can satisfy other cybersecurity requirements. For example, the Cybersecurity Maturity Model of Certification (CMMC) for Department of Defense contractors and subcontractors requires cloud providers to have FedRAMP authorization of Moderate or higher.
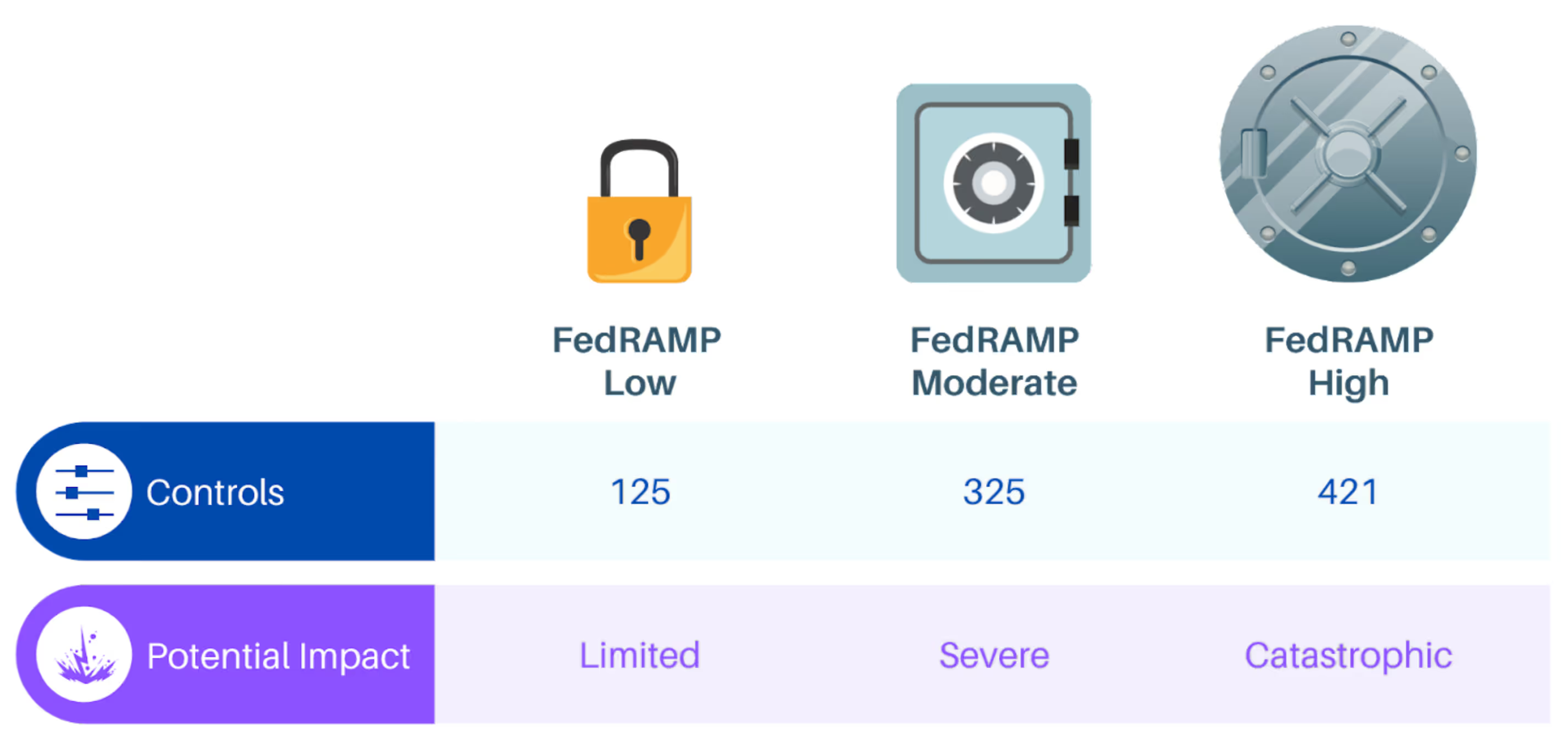
Controls required to meet FedRAMP standards include:
The higher the potential impact of compromised data, the more controls are required. These controls provide vital risk management for cloud service providers of all sizes.
Any CSP that stores, processes, or transmits federal data must meet the security standards for the appropriate FedRAMP impact level. Even cloud service providers who do not work with federal data can use FedRAMP standards to audit data integrity and improve security.
Unauthorized access to data, the destruction of data, or the disruption of data would have limited impact on the organization or individuals.
FedRAMP Low Impact Risk describes public use data, which can be “safely” compromised. Low Impact Risk is the lowest level of security that a cloud service provider should provide. There are two branches of FedRAMP Low Impact Risk: low baseline and the tailored low-impact Software-as-a-Service baseline.
Low-risk services have a streamlined authorization process. Within a low-risk environment, compromise could occur at any time without physical or financial detriment to the users of the service. An example of a FedRAMP Low Impact Risk service would be a service that provides purely informational data and does not store any personally identifiable user information.
Unauthorized access to data, the destruction of data, or the disruption of data would have a serious adverse impact on the organization or individuals.
FedRAMP Moderate Impact Risk describes the standards for controlled, unclassified information. Controlled, unclassified information includes personally identifiable information, such as a list of names, addresses, and email addresses.
If compromised, a FedRAMP Moderate Impact Risk system could cause moderate financial harm to individuals — such as identity theft. This level of security requires a baseline of 325 controls, including:
Unauthorized access to data, the destruction of data, or the disruption of data would have a severe or catastrophic adverse impact on the organization or individuals.
FedRAMP High Impact Risk governs sensitive, unclassified government information. Examples of FedRAMP High Impact Risk systems include those used by law enforcement, emergency services, and healthcare services. If these services were compromised, altered or disrupted, there could be significant financial or even physical harm to individuals.
FedRAMP High Impact Risk requirements include a total of 421 controls. It is the most challenging standard to meet — it requires that a system and its processes have sufficient controls to protect the most sensitive of unclassified government data.
FedRAMP isn’t the only cloud service security standard available. Other cloud security certifications include:
Specific industries frequently require companies to hold relevant security certifications. For example, CSPs in the healthcare industry can benefit from HITRUST certification, which provides a common benchmark for compliance.
Even if you aren’t handling federal data, FedRAMP’s impact levels can provide an excellent baseline to evaluate cloud security standards — and help mitigate risk for users.
For cloud service providers, FedRAMP impact levels make it easier to assess the levels of security needed relative to the potential risk of the data involved. By providing a list of detailed security controls, FedRAMP also provides an outline for auditing and improving security systems. At higher levels of privacy, higher levels of security are enforced. By correlating security levels to the potential impact of exposure, FedRAMP puts user privacy and protection at the forefront of the security process.
Understanding cloud service providers’ FedRAMP certification provides security and peace of mind, especially if you develop applications for the public sector. For example, Salesforce Government Cloud Plus operates in the FedRAMP High Impact Risk category — the highest level of security available under the FedRAMP system.
However, you need to make sure your entire development pipeline complies with federal, state, and industry data protection requirements, including when data is in transit. Sponsored by the Department of Veteran Affairs, Copado is FedRAMP In Process and has a proven track record working with public sector entities, including the Department of Veteran Affairs, the state of California, District of Columbia, and the Province of Ontario. With Copado, government agencies can deliver solutions faster without sacrificing stability or good governance.
Explore our DevOps resource library. Level up your Salesforce DevOps skills today.

.avif)


.svg)
